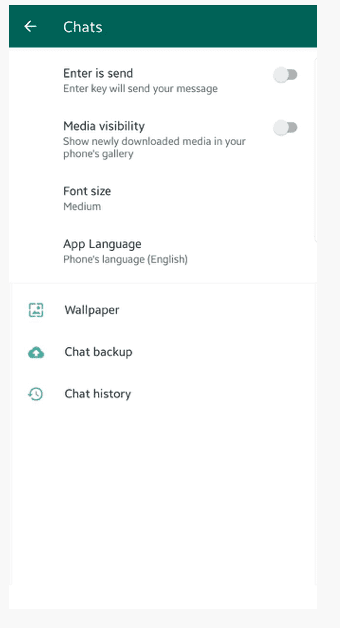
WhatsApp, Telegram Files Could be Hacked – ‘Media File Jacking’
‘Media File Jacking’ is the new buzzword phrase that describes a security flaw and enables hackers to manipulate images and audio files on various platforms, and in this case ‘end-to-end encryption’ apps WhatsApp and Telegram on Android. Symantec’s Modern OS Security team explained ‘neither apps have any system in place to protect users from a Media File Jacking attack’. “If the security flaw is exploited, a malicious attacker could misuse and manipulate sensitive information such as personal photos and videos, corporate documents, invoices, and voice memos,” wrote Software Engineer Alon Gat and Yair Amit, Vice-President and Chief Technology Officer, Modern OS Security, Symantec. ‘Media File Jacking’ is the new buzzword…